Author: Singh Amrit, Kansal Atulesh, NXP Semiconductors
With the increasing popularity of embedded electronic devices in automobiles and other products, the need for connectivity has increased. This connection may be a connection between on-board devices, or it may be a connection established by the SoC with the outside world through a wired or wireless network.
As a result, information security has become a key issue for car SoCs and it is crucial to ensure that information is not tampered with in transit. Security measures include encryption, digital signatures, MAC calculations, and authentication.
Security verification is not just a test function, but more importantly, testing a risk scenario or a security attack. When conducting security verification, testers must have hacking thinking and perspective. At present, many of the equipment used for safety testing are expensive. Several negative tests discussed in this paper do not require the use of such equipment and can be used in post-silicon verification.
The following are several ways to perform endurance testing on security based on scenarios and confrontation.
ECC detection
ECC failures can occur at any time in non-volatile memory, so we should understand the behavior of the device in the event of an ECC failure and check whether the failure has caused a security breach. For verification purposes, we can inject multiple bits of ECC error internally. Errors can be injected into nonvolatile memory, key areas, secure firmware, secure memory images, and device configuration registers.
For example, insert ECC in the memory that stores the security engine's output. The AES-128 engine will encrypt two 128-bit data blocks. In this case, there are two ECC scenarios:
1. ECC inserts the first 128-bit data block, and the rest of the memory is accessible. We can use this test to confirm that when the first data block has an error, the security engine will either terminate the encryption of the next data block or ignore the error and save the output of the second accessible data block.
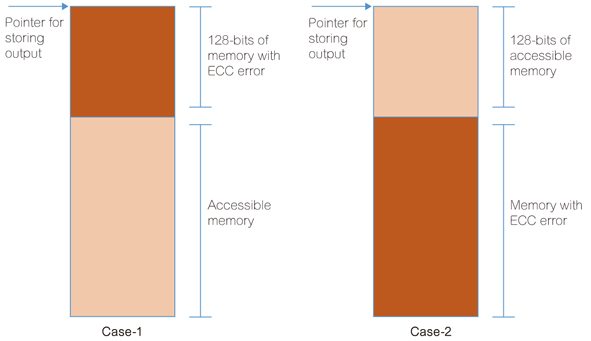
Figure 1: Two scenarios for inserting ECC in the memory of the Security Engine output.
2. The first 128 bits of memory are accessible and ECC inserts the next 128-bit data block. We can confirm through this test whether the first data block is stored in the accessible memory and the operation is terminated when an error occurs in the second data block, or whether the operation of both data blocks is terminated.
Order sorting and cancellation
Check the device behavior by controlling the order in which the commands are executed. For example, a valid encryption/decryption command is executed after an invalid command is executed. This situation is to ensure that if an error occurs due to the execution of an invalid command, if a valid encryption/decryption command is executed again, the error no longer exists.
Cancel: The cancel/abort command was issued during operation. Incomplete output should not be generated to avoid leakage of security data. Other safety operations can also be checked in the same way.
Clock tampering
The clock is crucial for ensuring security. Multiple scenes can be detected:
1. In theory, it should not be specified that clock gating is only deployed for secure IP.
2. If it is specified to deploy clock gating to secure IPs, then try to perform during security operations and ensure that clock gating does not cause security data leakage or key leakage.
3. If a microcontroller contains multiple secure IPs and clock gating is to be deployed for each IP, be sure to check all possible permutations/combinations of clock gating. This will ensure that any secure IP gating will not affect other secure IPs and will not cause the security data to leak.
4. If the security module is equipped with a clock divider, check all of these dividers to ensure that the operation meets the desired level of security.
5, clock tamper may also include changing the frequency of the security module, and the frequency value is set to a value outside the specified frequency range, and then cause a failure.
Voltage change
The supply voltage adjustment can affect the performance of the equipment and safety modules. But even changing the voltage should not affect the operation of the equipment. Try the following scenario:
â—? When the equipment operating voltage is the specified minimum voltage or maximum voltage, perform safety operations.
â—? When the operating voltage of the equipment is higher or lower than the specified voltage, perform safety operations.
â—? The voltage is suddenly changed to a value outside the specified range during safety operation.
â— The voltage suddenly changes during safe operation.
â— Change the voltage gradually during safe operation.
Asynchronous event generation
SoC supports different types of asynchronous events, such as unmasked interrupts, power operating mode changes, and so on. Testing these asynchronous events is crucial for security engine verification. For example, a low-power mode request is triggered during some safety operations and then returns to normal mode. This should not lead to leakage of safety data.
Asynchronous event scanning
Next, asynchronous events are applied at different intervals of the security operation. This operation can help us determine that events that occurred at random intervals or random power consumption did not result in the disclosure of security data or the disclosure of security keys. You can try asynchronous event scanning during operations such as secure boot, encryption/decryption, and generate/verify signatures.
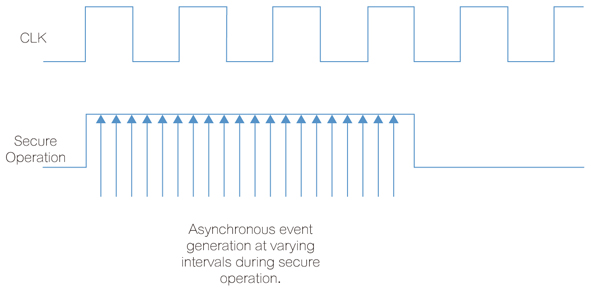
Figure 2: Asynchronous events are generated at different time intervals during safe operation.
Asynchronous events can be generated at different time intervals within different or same power cycles, and the time windows generated by the events can be expanded or reduced.
Other attack methods
â—? Try to expose security information through the debug port in a variety of ways.
â—? Software attack: execution of malicious code (any non-application code).
â— Try to destroy a random or non-safe area, and confirm that there is no leakage of security information.
in conclusion
Security verification cannot be exhaustive, and there are always methods of interfering with the equipment that can cause leakage of security information. The purpose of security verification is not to check whether the device is working properly, but to find out that the device may be attacked so as to prevent it from happening.
KNM1 Series Moulded Case Circuit Breaker
KNM1 series Moulded Case Circuit Breaker is MCCB , How to select good Molded Case Circuit Breaker suppliers? Korlen electric is your first choice. All moulded Case Circuit Breakers pass the CE.CB.SEMKO.SIRIM etc. Certificates.
Moulded Case Circuit Breaker /MCCB can be used to distribute electric power and protect power equipment against overload and short-current, and can change the circuit and start motor infrequently. The application of Moulded Case Circuit Breaker /MCCB is industrial.
Korlen electric also provide Miniature Circuit Breaker /MCB. Residual Current Circuit Breaker /RCCB. RCBO. Led light and so on .
KNM1 series Molded Case Circuit Breaker,KNM1 series Small Size Molded Case Circuit Breaker,KNM1 series Electrical Molded Case Circuit Breaker,KNM1 series Automatic Molded Case Circuit Breaker
Wenzhou Korlen Electric Appliances Co., Ltd. , https://www.zjmotorstarter.com